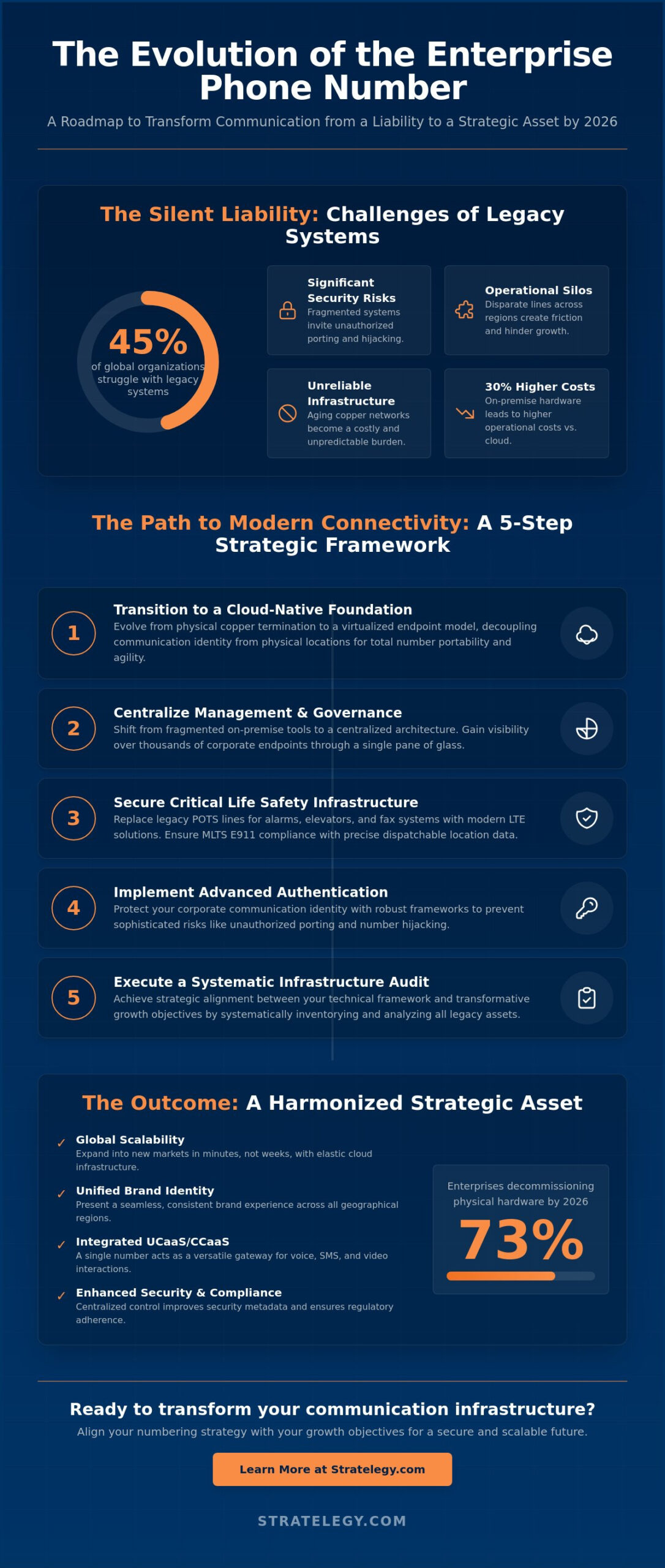
Is your most basic communication tool actually a silent liability? While many executives view the enterprise phone number as a mere utility, data suggests that 45% of global organizations still struggle with fragmented legacy systems that invite security risks and operational silos. You likely feel the friction of managing thousands of disparate lines across various regions, especially as the unreliability of aging copper infrastructure becomes a costly burden on your bottom line. We understand that maintaining order in a complex global environment requires more than just technical fixes; it demands a vision for strategic alignment.
This article promises to show you how to evolve your numbering strategy into a sophisticated asset for global connectivity and critical life safety. We’ll outline a roadmap for 2026 that replaces chaos with a unified, scalable framework. You’ll learn how to achieve seamless integration between voice, video, and messaging while ensuring compliance with modern safety standards. By the end of this guide, you’ll have the blueprint to transform your infrastructure into a harmonized system that drives both security and transformative growth.
Key Takeaways
- Master the transition from physical copper termination to a virtualized endpoint model, evolving your communication assets into a cloud-native foundation for global connectivity.
- Secure your critical life safety infrastructure by replacing legacy POTS lines, ensuring your phone number ecosystem remains resilient as traditional landline support nears its end.
- Implement advanced authentication and governance frameworks to protect your corporate communication identity from the sophisticated risks of unauthorized porting and hijacking.
- Execute a systematic audit of your legacy infrastructure to achieve strategic alignment between your technical framework and your organization’s transformative growth objectives.
- Shift from fragmented on-premise management to a centralized cloud-native architecture that transforms thousands of corporate endpoints into a harmonized and scalable strategic asset.
The Strategic Evolution of the Business Phone Number
In the sophisticated ecosystem of 2026, a phone number is no longer a static terminal tied to a copper wire. It has evolved into a virtualized endpoint, a digital anchor within a global network that transcends physical boundaries. This transformation marks the definitive shift from hardware dependency to cloud-based identity. For multi-national organizations, the strategic alignment of these numbering assets isn’t merely a technical requirement; it’s a foundational element of brand authority. When an enterprise synchronizes its global numbering, it creates a seamless interface for clients, partners, and internal teams alike.
The Public Switched Telephone Network (PSTN) continues to play a vital role in this era. While often viewed as a legacy system, it serves as the high-availability gateway that ensures universal reach. Architecting a scalable infrastructure requires a deep understanding of the global telephone numbering plan, which dictates how resources are allocated across international borders. By 2025, industry data indicated that 91% of Global 2000 firms had successfully integrated their PSTN access with cloud-native identity layers, ensuring that every digit serves a strategic purpose.
From Hardware Dependency to Digital Identity
Modern enterprises have decoupled their communication identity from physical locations. This shift allows for total number portability, which is essential for maintaining brand continuity during rapid expansion or organizational restructuring. Legacy thinking, which views a phone number as a fixed asset tied to a local switch, limits agility. It creates silos that hinder growth. In contrast, a digital identity approach offers several advantages:
- Elasticity to scale operations into new markets within minutes rather than weeks.
- Unified brand presentation across diverse geographical regions.
- Centralized management of communication metadata for improved security.
Organizations that cling to on-premise hardware often face 30% higher operational costs compared to those utilizing cloud-native identity frameworks. The move to virtualized endpoints isn’t just about efficiency; it’s about reclaiming control over the corporate persona.
The Role of Numbers in Unified Communications (UCaaS)
A single number now functions as a versatile gateway for voice, SMS, and video interactions. This convergence requires integrating numbering into a customized framework that aligns with specific business workflows. Instead of managing disparate systems for different media, the enterprise treats the number as a singular point of contact. This level of integration ensures that the flow of communication remains rhythmic and purposeful, reflecting the brand’s commitment to professional excellence. UCaaS-integrated numbering serves as the backbone of modern collaboration.
Architecting a Scalable Enterprise Numbering Framework
The evolution from on-premise PBX systems to cloud-native UCaaS and CCaaS architectures represents a fundamental shift in corporate connectivity. By 2026, 73% of global enterprises will have decommissioned their physical hardware in favor of elastic, software-defined environments. This transition demands a move from fragmented, site-specific management to a centralized framework that governs every corporate phone number across the organization. Consolidating legacy providers transforms operational chaos into a structured asset; it allows IT leaders to reclaim visibility over thousands of disparate endpoints through a single pane of glass.
Safety and compliance remain the bedrock of this architecture. Modern systems must strictly adhere to FCC requirements for MLTS, ensuring that every cloud-based extension provides precise dispatchable location data for emergency services. This regulatory alignment is not merely a legal hurdle. It is a critical component of a resilient life-safety strategy that protects employees regardless of their physical location. Intelligent routing further elevates this framework by transforming how calls traverse the network, ensuring that every interaction is directed by logic rather than geography.
Global Reach and Local Presence
Establishing trust in a fragmented global market requires a sophisticated approach to local numbering. Data from 2024 industry reports indicates that 78% of customers are more likely to engage with an organization that displays a familiar area code. Managing international numbering through a unified cloud gateway eliminates the need for physical branch offices while maintaining low-latency voice termination. This strategic alignment ensures that voice packets travel the shortest path possible, maintaining crystal-clear audio quality across continents and cultures.
CCaaS Integration for Enhanced CX
In the modern enterprise, a phone number serves as the primary data entry point for sophisticated customer journey analytics. When a call enters the CCaaS environment, intelligent routing engines immediately cross-reference the dialed number against CRM data to provide agent-assist AI with real-time context. This creates a harmonious flow between automated IVR systems and human professionals. Organizations that implement these tailored frameworks see a 22% improvement in first-call resolution rates. To achieve this level of operational elegance, leaders must prioritize the strategic coordination of their digital assets.
Critical Infrastructure: LTE POTS Replacement for Life Safety
Legacy copper lines represent a silent vulnerability in modern enterprise safety protocols. While many organizations focus on cloud migration for customer-facing voice services, they often overlook the critical phone number connections tied to fire panels and elevator shafts. Major carriers are aggressively decommissioning these circuits, with industry projections indicating a total cessation of traditional landline support by 2029 following FCC Order 19-72. This transition isn’t merely a technical upgrade; it’s a strategic necessity to prevent catastrophic communication failure during emergencies. Relying on deteriorating copper infrastructure introduces risks that sophisticated enterprises can no longer afford to carry.
The Crisis of Aging Copper Infrastructure
Maintenance costs for legacy Plain Old Telephone Service (POTS) have surged by over 450% since 2019 as specialized technicians become scarce and physical hardware fails. This fiscal pressure, combined with falling reliability, has accelerated the transzformatív shift to LTE-based communicators. Modern “POTS in a box” solutions provide a resilient bridge, converting analog signals into digital packets while maintaining the physical interface required by legacy hardware. These systems represent the gold standard for business continuity, offering battery backups and cellular redundancy that traditional lines simply can’t match. By adopting these frameworks, leaders achieve a strategic alignment between heritage safety systems and modern digital resilience.
Reliability Requirements for Fire and Security
Fire and security systems require uncompromising uptime that legacy infrastructure can’t guarantee. Dual-path cellular monitoring creates a redundant architecture where signals travel through multiple carrier networks simultaneously, ensuring that a single tower failure doesn’t compromise the site. This level of resilience aligns with the NIST VoIP Security Guidelines, which emphasize the importance of robust, authenticated transmission paths for critical infrastructure. Modernizing elevator emergency phones is equally vital to meet updated ADA codes and ASME A17.1 standards, which mandate clear communication during extended power outages.
The strategic migration of every phone number associated with a life safety device ensures that emergency responders remain connected regardless of local utility conditions. Organizations must move beyond reactive maintenance to a proactive, testable framework of connectivity. Every enterprise must recognize the necessity of LTE backup for critical life safety endpoints to maintain regulatory compliance and human safety. This disciplined approach transforms a hidden liability into a pillar of institutional stability, ensuring that the most vital lines are the most reliable ones in the building.
Security and Governance of Corporate Communication Identity
In 2026, a corporate phone number represents more than a contact point; it’s a verified digital identity. Criminal entities target the B2B sector through sophisticated number hijacking, where unauthorized porting requests can divert critical business traffic in minutes. This vulnerability demands a posture of calm professionalism rather than reactive panic. We must move toward strategic alignment between telecommunications and cybersecurity frameworks. Implementing Multi-Factor Authentication (MFA) for porting requests and Port Out PINs has become the baseline for securing these assets.
The industry’s defense rests on the STIR/SHAKEN framework. Since the FCC’s June 30, 2021, mandate for large carriers, the protocol has evolved to combat AI-driven spoofing. By 2025, 92% of top-tier enterprise carriers integrated advanced attestation levels, ensuring that when your organization calls a client, the identity displayed is untampered and authoritative. Maintaining this trust requires a meticulous approach to how identity is broadcasted across global networks.
Protecting Your Brand’s Voice Identity
Vetting providers requires a rigorous evaluation of their redundancy and encryption standards. Secure virtual faxing remains a cornerstone for industries like healthcare, where HIPAA compliance dictates that every phone number used for document transmission must adhere to AES-256 encryption. Annual audits are no longer optional. Organizations should conduct quarterly inventory reviews to identify “ghost numbers” that increase the attack surface without providing value. This systematic pruning ensures that your communication perimeter remains tight and manageable.
Disaster Recovery and Business Continuity
Resilience is built on the assumption of failure. When primary fiber connections fail, enterprise-grade cellular routers using 5G technology provide an immediate bridge to maintain connectivity. Modern CCaaS platforms now target “five nines” (99.999%) availability, but true continuity depends on automated failover strategies. If a regional outage occurs, your infrastructure should dynamically reroute traffic to secondary SIP trunks without manual intervention. This ensures the brand remains reachable, projecting stability during external chaos. A well-designed phone number strategy accounts for these contingencies long before they occur.
Executing Your Strategy: The Path to Modern Connectivity
Transitioning to a 2026-ready infrastructure requires more than a software update; it demands a fundamental shift in how your organization views its communication assets. Execution begins with a rigorous audit of legacy systems. Data from 2024 indicates that 65% of large enterprises still pay for redundant analog circuits that serve no modern purpose. A comprehensive audit should include a full inventory of active DID ranges, a map of all PSTN handoffs, and a review of existing SIP trunking utilization rates. This clarity prevents the migration of “ghost” costs into your new cloud environment.
Selecting a partner involves finding deep strategic alignment. You aren’t just looking for a vendor to port a phone number; you’re seeking an architect who understands how communication flows through your specific business logic. Stratelegy positions itself as this architect, turning chaotic legacy setups into refined, high-performance ecosystems. Our implementation roadmap follows a disciplined 4-phase cycle: discovery, a 90-day pilot program for high-impact departments, a phased migration of core services, and a final optimization phase to ensure 99.999% reliability across all touchpoints.
The Stratelegy Approach to UCaaS and LTE
We bridge the gap between aging hardware and cloud-native potential by providing clean solutions for inherently complex problems. Our framework integrates UCaaS flexibility with the robust reliability of LTE failover, ensuring that your enterprise stays connected during localized outages. We place equal weight on high-volume CCaaS environments and critical life safety systems. This dual focus ensures that your transition to the cloud doesn’t compromise E911 compliance or emergency response protocols, maintaining architectural harmony across your entire network.
Next Steps for Enterprise Leaders
The journey toward a unified communication landscape starts with preparation. Leaders should prioritize team readiness by identifying internal champions who can advocate for the new system’s efficiency. You can begin this process today by requesting a comprehensive infrastructure audit to uncover hidden inefficiencies in your current stack. This data-driven approach removes the guesswork from your digital transformation. When you’re ready to move beyond simple digits and toward a vision of integrated connectivity, Partner with Stratelegy to modernize your communication strategy.
Architecting the Future of Enterprise Connectivity
The transition from legacy copper to modern digital infrastructure isn’t just a technical upgrade; it’s a strategic necessity for the 2026 business landscape. Organizations must prioritize the migration of life safety systems through LTE POTS replacement to ensure total compliance with evolving safety mandates. Securing your corporate identity starts with a unified phone number framework that integrates seamlessly with your UCaaS and CCaaS ecosystems. This strategic alignment transforms a basic communication tool into a resilient asset for global operations.
True connectivity demands a balance between technical precision and visionary planning. By modernizing your B2B infrastructure today, you eliminate the risks of fragmented governance and aging hardware. It’s about creating a structure where every touchpoint reflects your brand’s authority. Stratelegy provides the sophisticated oversight required for complex transitions and life safety migrations. Let’s build a future where your communications are as refined as your business objectives.
Design your enterprise communication strategy with Stratelegy
Frequently Asked Questions
What is the difference between a traditional phone number and a VoIP number?
A traditional phone number relies on physical copper circuits, while a VoIP phone number transmits data packets over a broadband connection. This shift enables a tailored framework where communications aren’t tethered to a specific desk. Modern VoIP systems achieve 99.999% uptime, providing a level of resilience that legacy systems can’t match in a globalized business environment.
Why are POTS lines being phased out for fire alarms and elevators?
POTS lines are being retired because the FCC Order 19-72 removed the requirement for carriers to maintain aging copper infrastructure. Maintenance costs for these legacy lines have surged by 450% in some markets since 2019. Modern life-safety systems now utilize LTE-M technology to ensure fire alarms and elevators remain connected with superior 24-hour battery backup and supervised signaling.
Can I keep my existing business phone numbers when moving to the cloud?
You can certainly keep your existing identifiers through the Local Number Portability process. Federal regulations ensure you own your numbers, allowing for a seamless transition that typically takes 7 to 14 business days. This strategic alignment preserves your established brand equity while moving your operations into a more flexible, cloud-based environment without any disruption to client access.
How does LTE POTS replacement ensure better reliability than copper?
LTE POTS replacement offers 99.9% reliability by using dual-carrier SIM cards to provide instant failover if one network falters. Copper wires are vulnerable to physical decay and water ingress, which accounted for 30% of system failures in 2023. These wireless solutions include internal batteries that sustain emergency operations for 24 hours, exceeding the performance of traditional analog lines.
What security measures protect enterprise phone numbers from being hijacked?
Enterprises secure a phone number by implementing Multi-Factor Authentication and dedicated Port-Out Pins at the carrier level. Using a Registry Lock adds another layer of defense against unauthorized transfer attempts. These protocols helped reduce identity hijacking by 60% in the enterprise sector during 2023, ensuring that your core communication assets remain under your exclusive control.
How does a unified numbering strategy improve customer engagement?
A unified numbering strategy improves engagement by presenting a consistent brand identity across voice, SMS, and digital channels. Research from 2024 indicates that customers are 40% more likely to engage with a recognized local number than an anonymous or toll-free source. This approach transforms every interaction into a sophisticated touchpoint that reinforces trust and professional authority.
What is the cost impact of switching from legacy lines to an LTE-based system?
Transitioning to LTE-based systems typically reduces monthly operational costs by 40% to 60% compared to traditional analog lines. While there’s an initial hardware cost, most enterprises see a full return on investment within 12 to 18 months. Industry data shows that the cost of maintaining legacy copper is rising by 20% annually, making the move a prudent financial decision.
Is virtual faxing as secure as traditional fax machines for sensitive data?
Virtual faxing is significantly more secure than traditional machines because it utilizes AES-256 encryption for every transmission. Physical fax machines often leave sensitive documents exposed on open trays, which led to numerous compliance risks in the past. Cloud-based solutions provide a complete digital audit trail, ensuring that 100% of your data remains protected and compliant with modern privacy standards.

